
This episode of Ship It Weekly delves into Cloudflare's BYOIP outage, highlighting how automation can lead to unintended BGP withdrawals, and Clerk's performance issues from a query plan flip in Postgres.

Transcript
Catch This Episode
Listen on your favorite podcast platform
Host Commentary
For this episode, I wanted to anchor on something I think every ops team learns the hard way.
The incidents that hurt the most are rarely the big obvious deploys.
It’s the background systems. The reconcilers. The cleanup jobs. The “this should be safe because it’s routine” automation.
Because those jobs are usually touching shared truth.
Routing state. Prefix state. Permissions. Database statistics. The stuff everything else quietly depends on.
And when that shared truth shifts under you, you don’t just get a bug. You get reachability problems. You get cascading retries. You get queueing. You get “everything is up but nothing works.”
Cloudflare BYOIP is the cleanest example this week.
This wasn’t “somebody fat-fingered BGP.” It was a buggy cleanup sub-task that queried the Addressing API wrong and ended up withdrawing about 1,100 BYOIP prefixes before they could revert the change. Some customers could re-advertise their prefixes from the dashboard, but the real work was restoring prefix configuration state back to normal.
That’s the lesson. If you have automation that can touch reachability, it is production control plane. Treat it like prod deploy tooling, not like “just a job.” Put caps on it. Put canaries on it. Put a circuit breaker on it. And most importantly, build rollback that does not require tribal knowledge at 3am.
Cloudflare outage postmortem
https://blog.cloudflare.com/cloudflare-outage-february-20-2026
Next, Clerk’s postmortem is the same theme, just inside Postgres instead of BGP.
Auto analyze ran, statistics shifted, a query plan flipped into something awful, and suddenly the system is shedding load so hard that most traffic is coming back 429 without even being handled. They fixed it by forcing ANALYZE again, and then they got really explicit about hardening failover so it can trigger on “any failure at origin,” not just “Postgres is down.”
This is why I keep saying “degraded is harder than down.”
Most teams have alarms for dead things. A lot fewer teams have alarms for “same query, different plan” or “latency is spiking but nothing is technically failing.” That gap is where the really ugly incidents live.
Clerk outage postmortem
https://clerk.com/blog/2026-02-19-system-outage-postmortem
And then you’ve got the AWS Kiro story, which is going to get summarized everywhere as “AI took down AWS.”
AWS’s response is basically: no, it was misconfigured access controls, and they added safeguards like mandatory peer review for production access. Reuters covered the reporting around it, and AWS published their own statement pushing back.
Here’s my take.
Whether it was an agent or a bash script, it’s the same root problem: a tool got permissions it shouldn’t have had.
So the practical move is boring, but it’s the whole game.
Separate propose from execute.
Let tools draft plans, diffs, PRs, and recommendations all day long.
But when it comes to destructive actions, make that path intentionally gated, intentionally scoped, and painfully auditable.
AWS response on Kiro
https://www.aboutamazon.com/news/aws/aws-service-outage-ai-bot-kiro
AWS outage reporting (Reuters)
Quick platform note before we move on.
AWS open-sourced the EKS Node Monitoring Agent, which is aimed at detecting node-level issues and surfacing them as signals EKS can act on, including automated node repair paths. This is one of those “make the pager quieter” features that I actually like seeing.
EKS Node Monitoring Agent
https://aws.amazon.com/about-aws/whats-new/2026/02/amazon-eks-node-monitoring-agent-open-source
Lightning round quick thoughts.
Grafana has a high severity issue where a user with permission management rights on one dashboard could modify permissions on other dashboards. If you run Grafana in a shared org and you’ve got a lot of teams in there, that’s a “patch it” item.
https://grafana.com/security/security-advisories/cve-2026-21721
AWS published a bulletin on runc CVEs affecting container runtime behavior when launching new containers. The evergreen reminder is still true: containers are not a security boundary, and runtime bugs turn into host risk depending on how you’re running workloads.
https://aws.amazon.com/security/security-bulletins/rss/aws-2025-024
GitLab shipped patch releases 18.6.1, 18.5.3, 18.4.5. If you self-host GitLab, you already know the rule. Staying behind becomes “we’ll do it later” until it becomes a weekend incident.
https://about.gitlab.com/releases/2025/11/26/patch-release-gitlab-18-6-1-released
And Atlassian’s February bulletin is the monthly reminder that on-prem Data Center products are a patch treadmill. They call out a pile of high severity vulns and critical severity ones fixed in newer versions.
https://confluence.atlassian.com/security/security-bulletin-february-17-2026-1722256046.html
Human closer.
ACM Queue ran a piece called “SRE Is Anti-Transactional,” and it’s basically describing the exact emotional arc behind all of these stories.
SRE and platform teams aren’t trying to dodge work.
They’re trying to move the org away from manual, transactional toil, toward systems that do safe work by default, and only involve humans for exceptions.
But this week is a reminder that you don’t get autonomy by giving tools more power.
You get autonomy by engineering the guardrails first, then widening the lane over time.
SRE Is Anti-Transactional
https://queue.acm.org/detail.cfm?id=3773094
That ties the whole episode together.
Cloudflare automated cleanup touching routing state.
Clerk got hit by a “system is up but behavior changed” database failure mode.
AWS is reinforcing that permissions are still the sharp edge, no matter what tool is holding the knife.
Defaults shift. Background systems become dependencies. Guardrails decide whether it’s a story you learn from, or a story you apologize for.
Full show notes are on shipitweekly.fm. The weekly curated brief is on oncallbrief.com.
And if you got value out of this episode, follow or subscribe wherever you listen. Helps a ton.
Show Notes
This week on Ship It Weekly, Brian looks at how the boundary of ops keeps expanding.
We cover AWS flagging issues in Bahrain/UAE amid Iran strikes, ArgoCD vs Flux and why ArgoCD can get stuck in failed sync states, GitHub Actions being exploited at scale (plus Trivy’s incident), RoguePilot prompt injection meeting real credentials in Codespaces, Block’s “AI remake” layoffs, and Anthropic’s Claude Code Security for defenders.
Lightning round: DeepSeek model access geopolitics, Vercel’s agentic security boundaries, a KEV CVE to patch, an MCP-atlassian SSRF-to-RCE chain, and Claude Cowork scheduled tasks.
Links
AWS Bahrain/UAE (Reuters) https://www.reuters.com/world/middle-east/amazon-cloud-unit-flags-issues-bahrain-uae-data-centers-amid-iran-strikes-2026-03-02/
ArgoCD to Flux https://hai.wxs.ro/migrations/argocd-to-flux/
GitHub Actions exploitation https://www.stepsecurity.io/blog/hackerbot-claw-github-actions-exploitation
Trivy incident https://github.com/aquasecurity/trivy/discussions/10265
RoguePilot https://thehackernews.com/2026/02/roguepilot-flaw-in-github-codespaces.html
Block layoffs (WSJ) https://www.wsj.com/business/jack-dorseys-block-to-lay-off-4-000-employees-in-ai-remake-28f0d869
Claude Code Security https://www.anthropic.com/news/claude-code-security
DeepSeek (Reuters) https://www.reuters.com/world/china/deepseek-withholds-latest-ai-model-us-chipmakers-including-nvidia-sources-say-2026-02-25/
Agentic boundaries https://vercel.com/blog/security-boundaries-in-agentic-architectures
mcp-atlassian CVE https://arcticwolf.com/resources/blog-uk/cve-2026-27825-critical-unauthenticated-rce-and-ssrf-in-mcp-atlassian/
Claude Cowork tasks https://support.claude.com/en/articles/13854387-schedule-recurring-tasks-in-cowork
More: https://shipitweekly.fm
More from Ship It Weekly
All episodes →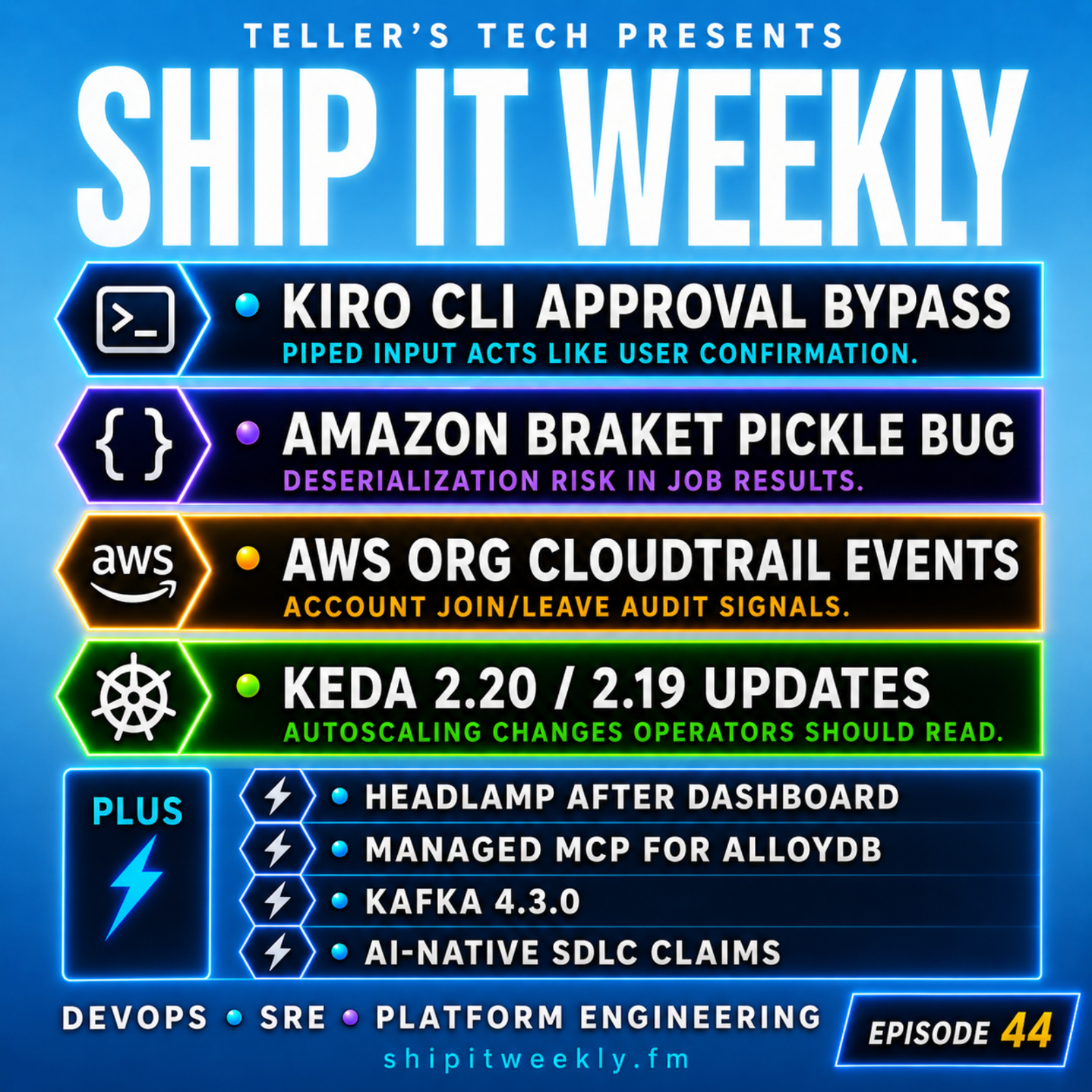
Kiro CLI Approval Bypass, Amazon Braket Pickle Risk, AWS Org Logging, KEDA Upgrades, and Automation’s Hidden Boundaries
This episode of Ship It Weekly explores automation's hidden boundaries, focusing on Kiro CLI's CVE-2026-9255 approval bypass and Amazon Braket's Python pickle risk.

GitHub Supply Chain Attacks, Railway’s GCP Outage, Discord’s Voice Failure, AWS Retry Changes, and Trusted Tool Risk
This episode of Ship It Weekly discusses the growing risks of trusted tools in production, highlighted by a GitHub supply chain attack involving a compromised VS Code extension.

Ship It Conversations: Jake Warner on Cycle.io, Bare Metal’s Comeback, and Why Private Cloud Is Getting Interesting Again
In this episode, Jake Warner of Cycle.io discusses the resurgence of bare metal and private cloud, emphasizing their benefits in cost, performance, and compliance.
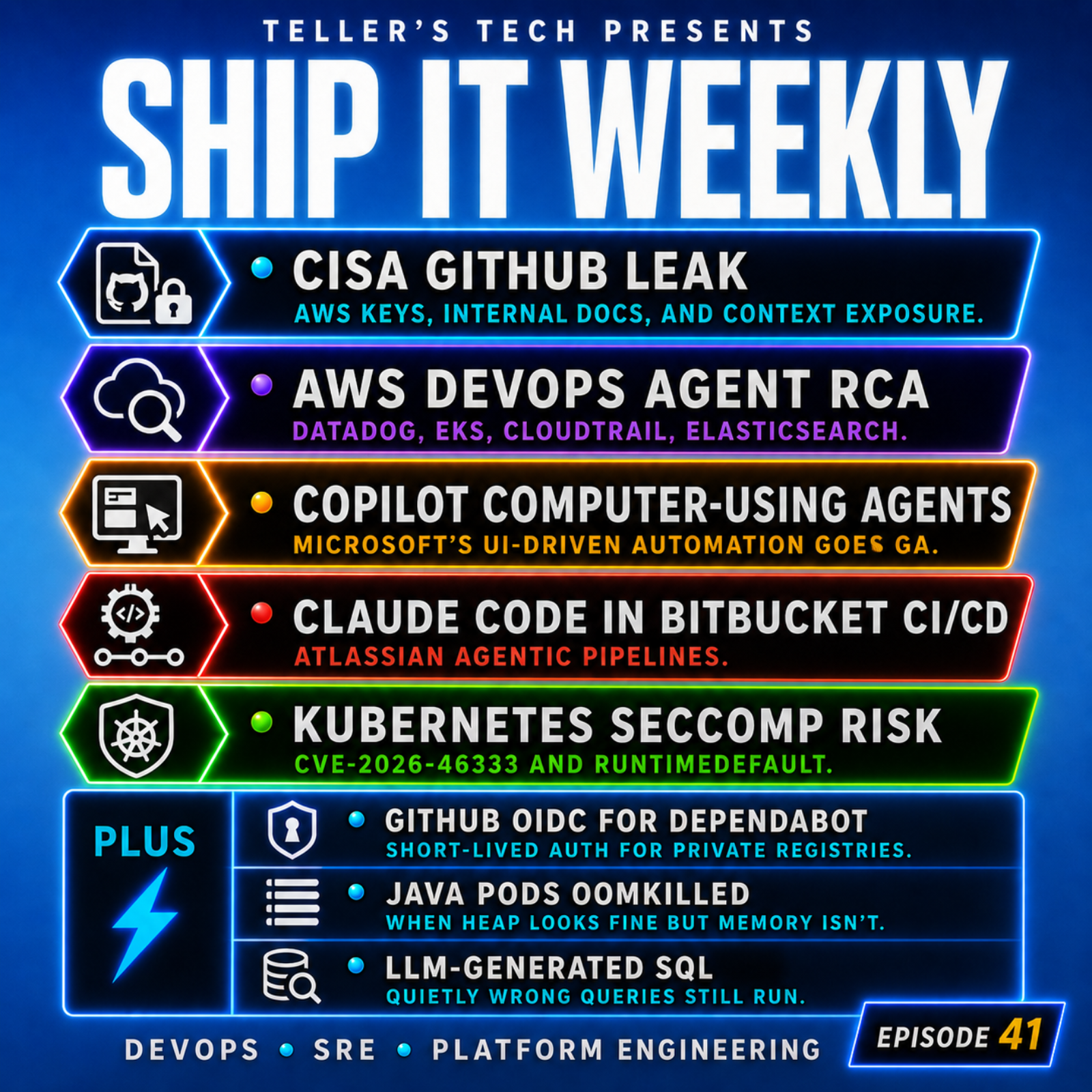
CISA’s GitHub Leak, AI Root Cause Analysis, Copilot Agents, Claude Code in CI/CD, and Kubernetes Seccomp Risk
This episode of Ship It Weekly discusses the implications of the CISA GitHub leak, highlighting the exposure of AWS keys and internal documentation.
