
In this episode of Ship It Weekly, Brian discusses significant shifts in operational defaults affecting DevOps teams. Topics include GitHub's Agentic Workflows, Gentoo's migration to Codeberg, Argo CD's upgrade challenges, and AWS Config's expanded coverage.

Transcript
Catch This Episode
Listen on your favorite podcast platform
Host Commentary
For this episode, I wanted to anchor on something I think a lot of teams miss until it bites them.
The default behavior of the platforms we lean on is shifting.
Not in a “new feature, neat” way.
In a “this is how work happens now unless you intentionally opt out” way.
And ops pain almost always shows up when a default changes quietly, then becomes a dependency.
GitHub Agentic Workflows inside Actions is the clearest example.
It’s not “AI in the UI.” It’s “AI in the automation engine.”
That matters because Actions is where the permissions live, and where small scripts quietly become production processes.
The moment an agent can propose changes, run experiments, open PRs, retry, reroute, and generally keep iterating, you’ve moved from deterministic automation to goal-seeking automation.
That can be awesome, but the guardrails have to shift too.
If you treat it like a nicer YAML syntax, you’ll miss the real question.
“What is this allowed to change, and how do I prove what it changed?”
GitHub Agentic Workflows (preview)
https://github.blog/changelog/2026-02-13-github-agentic-workflows-are-now-in-technical-preview/
My practical take: start with “agents can propose, humans can merge.”
Make that the default until you have a reason to loosen it.
And do a permissions inventory first, not last.
Because if your workflows can write to the repo, publish releases, or touch environments, the blast radius is already there.
You’re just adding a smarter actor to the same set of keys.
Next, the Gentoo move to Codeberg.
This story isn’t just open source politics.
It’s a reminder that “the forge” is no longer a neutral place where code happens to live.
It’s now shaping behavior.
Policy decisions, product direction, incentive direction, even just the ambient pressure of “here’s the new recommended workflow.”
When a project like Gentoo moves, they’re basically paying a real cost to buy back optionality.
That’s a thing ops teams should recognize, because we deal with the exact same tradeoff in enterprises.
Convenience becomes dependency.
Dependency becomes lock-in.
Lock-in only becomes visible when the platform is degraded, changes direction, or becomes a risk you can’t explain away.
Gentoo moves to Codeberg
https://www.theregister.com/2026/02/17/gentoo_moves_to_codeberg_amid/
The practical move here is not “everyone should migrate off GitHub.”
It’s “know what you are renting.”
Your git remote is portable.
Your whole workflow often isn’t.
Issues, PR metadata, CI config, release automation, required checks, even your contributor and access model.
If you want leverage, you need at least one exit ramp.
Mirrors, backups, and a tested restore path are the boring version of freedom.
Then Argo CD 3.3 and the Server-Side Apply requirement.
This one looks like a technical detail, but it’s actually a reliability story.
Argo is your deployment system.
If you can’t upgrade it safely, you’re going to end up doing manual kubectl during a bad moment.
And the reason this upgrade note matters is it’s one of those “Kubernetes paper cuts” that turns into a real incident when you combine it with self-management patterns.
Annotation size limits are not exciting, but they’re exactly the kind of limit that surfaces at the worst time, and forces you into an emergency upgrade path.
Argo CD upgrade guide: 3.2 to 3.3 (SSA)
https://argo-cd.readthedocs.io/en/latest/operator-manual/upgrading/3.2-3.3/
My take: GitOps systems deserve an upgrade lane.
Treat Argo upgrades like you treat Kubernetes upgrades.
Rehearse them.
Diff live state vs what you think you apply.
And hunt down hand edits and “temporary overlays” before the upgrade does it for you.
SSA changes ownership semantics, and ownership semantics are where accidental overrides happen.
If you’ve ever said “we only changed one small thing in prod,” this is where that small thing disappears.
Next, AWS Config adding 30 new resource types.
This is the kind of change that’s easy to ignore because it feels like background.
But it’s exactly how governance scope creeps.
If you record “all resource types,” AWS can expand your inventory without asking.
That’s good coverage, but it can also mean new rule evaluations, new findings, new “noncompliant” noise, and new accountability questions.
And if you don’t have clear ownership, these tools don’t create governance.
They create a backlog.
AWS Config: 30 new resource types
https://aws.amazon.com/about-aws/whats-new/2026/02/aws-config-new-resource-types
My take: treat Config like a dataset you operate, not a checkbox.
Know if you are recording all resource types.
Baseline the rule surface.
And decide where findings route before they start routing to “whoever is awake.”
Also, this is where tagging and ownership metadata pays off.
Inventory is only useful when it’s attributable.
Otherwise, it’s just a bigger pile of “someone should fix this.”
Lightning round quick thoughts.
GitHub’s improved status page experience is genuinely nice.
It sounds small, but the best status pages aren’t the ones that look pretty, they’re the ones that answer “is this me or is it them” quickly.
And given GitHub’s hiccups lately, anything that makes the status view more usable is a win.
GitHub status page update
https://github.blog/changelog/2026-02-13-updated-status-experience/
The early-Feb Actions updates and the runner enforcement reminder are in that same category.
Not sexy, but operationally relevant.
The teams that keep things boring win long term.
Actions updates
https://github.blog/changelog/2026-02-05-github-actions-early-february-2026-updates/
Runner enforcement extended
https://github.blog/changelog/2026-02-05-github-actions-self-hosted-runner-minimum-version-enforcement-extended/
And the Open Build Service postmortem is worth reading if you’ve ever done “simple” migrations that turned out not simple.
If your migration plan doesn’t include rollback behavior under lock contention, degraded DB, or partial completion, you don’t have a plan yet.
You have hope.
Open Build Service postmortem
https://openbuildservice.org/2026/02/02/post-mortem/
Human closer.
The Lorin Hochstein post is the cleanest “smart take” I’ve seen lately on AI in ops.
Lots of AI SRE, no AI incident management.
That title is basically the whole point.
We’re getting tools that generate output.
Summaries, runbooks, postmortems, YAML, tickets.
That’s helpful, but it’s not the core pain of incidents.
Incidents are uncertainty and coordination.
What changed.
What’s real.
What’s correlated vs causal.
Who is driving.
What are we telling customers.
What are we rolling back and why.
If “AI for ops” doesn’t reduce uncertainty, it can accidentally increase chaos.
Because you’ll get more activity without more confidence.
You’ll get more suggestions without better verification.
You’ll get a faster loop that still depends on a tired human to decide what’s safe.
So my bar for AI tooling is simple.
Does it help a human make a safer decision faster.
Does it show its work.
Does it admit uncertainty.
Does it track actions taken, not just produce a narrative.
Because at 3am, a confident guess is worse than no guess.
Lots of AI SRE, no AI incident management
https://surfingcomplexity.blog/2026/02/14/lots-of-ai-sre-no-ai-incident-management/
That ties back to the whole episode.
Platforms are shifting defaults in ways that increase agency.
Agents inside CI.
Workflow and policy baked into the forge.
GitOps systems that require more careful ownership semantics.
Governance tools that expand scope automatically.
The work doesn’t go away.
It moves.
And the teams that do best are the ones that notice the default changed early, then operationalize it before it becomes an incident.
More episodes, plus the video playlist, weekly briefs, and Substack are all linked from here:
https://shipitweekly.fm
Show Notes
This week on Ship It Weekly, Brian hits five stories where the “defaults” are shifting under ops teams.
GitHub is bringing Agentic Workflows into Actions, Gentoo is migrating off GitHub to Codeberg, Argo CD upgrades are forcing Server-Side Apply in some paths, AWS Config quietly expanded coverage again, and EC2 nested virtualization is now possible on virtual instances.
Links
YouTube episodes https://www.youtube.com/watch?v=tuuLlo2rbI0&list=PLYLi5KINFnO7dVMbhsJQTKRFXfSSwPmuL&pp=sAgC
OnCallBrief https://oncallbrief.com
Teller’s Tech Substack https://tellerstech.substack.com/
GitHub Agentic Workflows (preview) https://github.blog/changelog/2026-02-13-github-agentic-workflows-are-now-in-technical-preview/
Gentoo moves to Codeberg https://www.theregister.com/2026/02/17/gentoo_moves_to_codeberg_amid/
Argo CD upgrade guide: 3.2 -> 3.3 (SSA) https://argo-cd.readthedocs.io/en/latest/operator-manual/upgrading/3.2-3.3/
AWS Config: 30 new resource types https://aws.amazon.com/about-aws/whats-new/2026/02/aws-config-new-resource-types
EC2 nested virtualization (virtual instances) https://aws.amazon.com/about-aws/whats-new/2026/02/amazon-ec2-nested-virtualization-on-virtual/
GitHub status page update https://github.blog/changelog/2026-02-13-updated-status-experience/
GitHub Actions: early Feb updates https://github.blog/changelog/2026-02-05-github-actions-early-february-2026-updates/
Runner min version enforcement extended https://github.blog/changelog/2026-02-05-github-actions-self-hosted-runner-minimum-version-enforcement-extended/
Open Build Service postmortem https://openbuildservice.org/2026/02/02/post-mortem/
Human story: AI SRE vs incident management https://surfingcomplexity.blog/2026/02/14/lots-of-ai-sre-no-ai-incident-management/
More episodes and show info on https://shipitweekly.fm
More from Ship It Weekly
All episodes →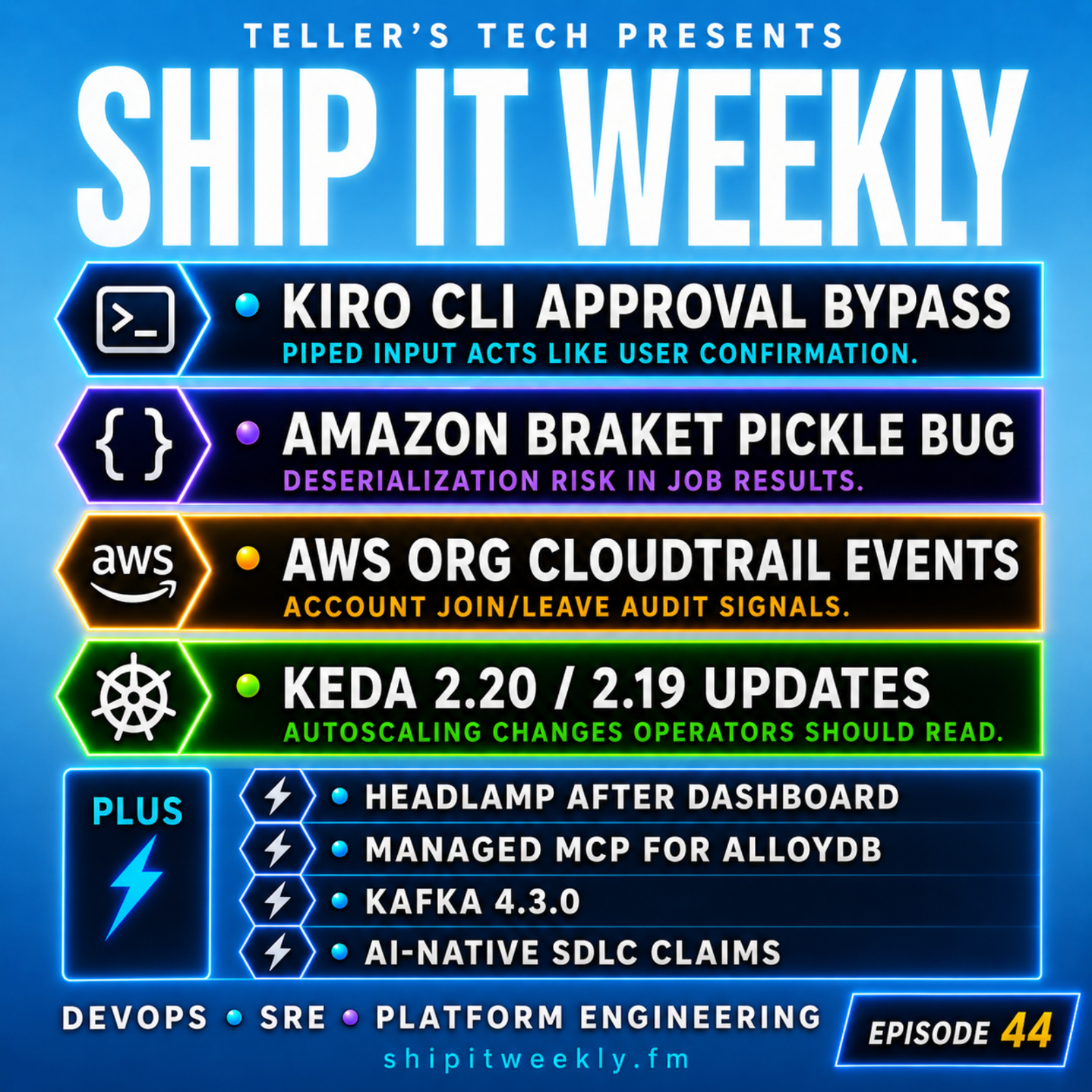
Kiro CLI Approval Bypass, Amazon Braket Pickle Risk, AWS Org Logging, KEDA Upgrades, and Automation’s Hidden Boundaries
This episode of Ship It Weekly explores automation's hidden boundaries, focusing on Kiro CLI's CVE-2026-9255 approval bypass and Amazon Braket's Python pickle risk.

GitHub Supply Chain Attacks, Railway’s GCP Outage, Discord’s Voice Failure, AWS Retry Changes, and Trusted Tool Risk
This episode of Ship It Weekly discusses the growing risks of trusted tools in production, highlighted by a GitHub supply chain attack involving a compromised VS Code extension.

Ship It Conversations: Jake Warner on Cycle.io, Bare Metal’s Comeback, and Why Private Cloud Is Getting Interesting Again
In this episode, Jake Warner of Cycle.io discusses the resurgence of bare metal and private cloud, emphasizing their benefits in cost, performance, and compliance.
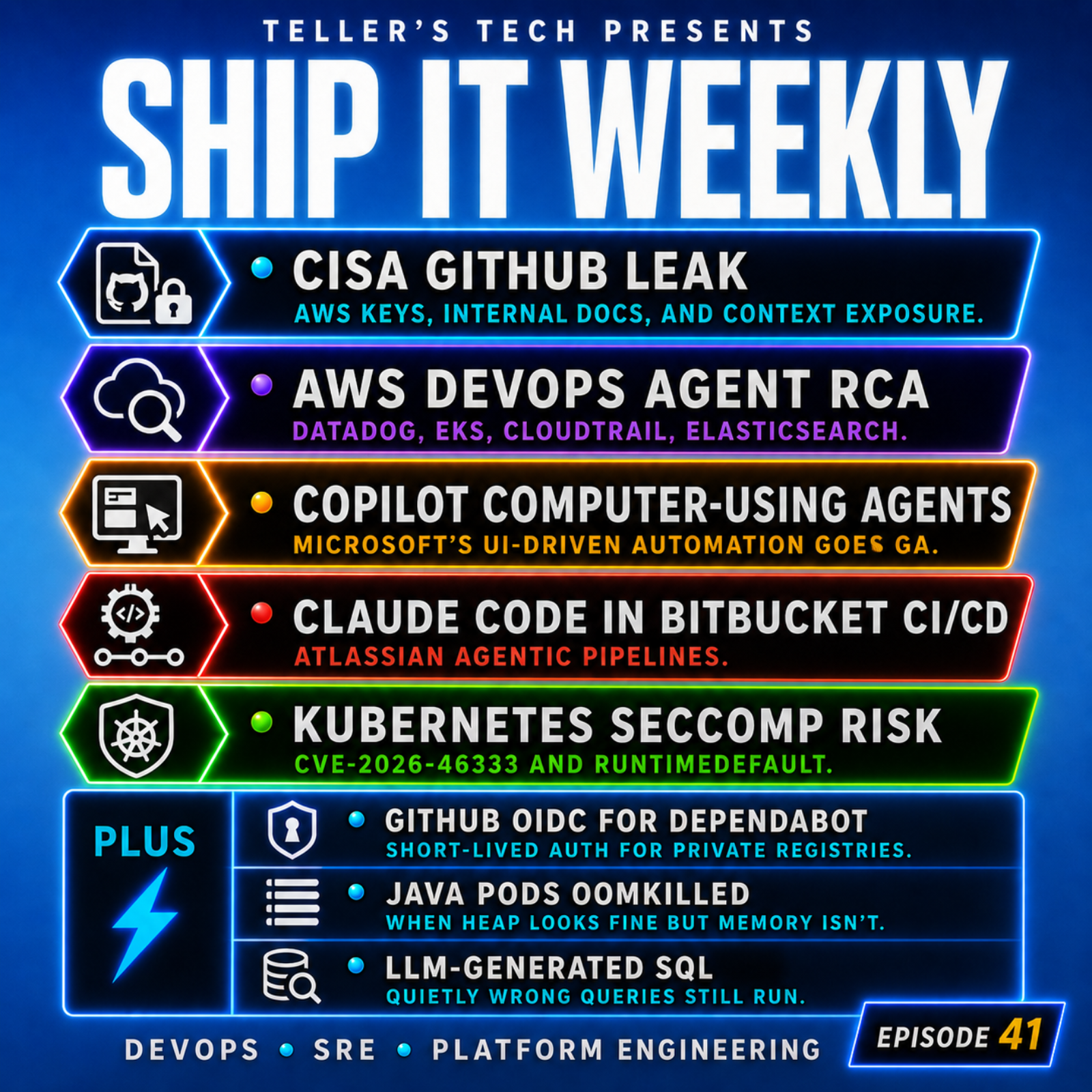
CISA’s GitHub Leak, AI Root Cause Analysis, Copilot Agents, Claude Code in CI/CD, and Kubernetes Seccomp Risk
This episode of Ship It Weekly discusses the implications of the CISA GitHub leak, highlighting the exposure of AWS keys and internal documentation.
