0:00
Picture this, not some vague future where AI
0:02
might matter to security someday. I mean right
0:05
now. What if the real shift is not that AI can
0:08
write code? What if the real shift is that it
0:11
can read a messy environment faster than your
0:14
organization can even decide who owns half of
0:17
it? Old services, stale images, forgotten runners,
0:21
broad IAM roles, weird sidecars, ancient dependencies,
0:25
a dashboard nobody meant to leave exposed. A
0:28
pipeline permission nobody wanted to untangle.
0:31
That is the frame for today. Hey, I'm Brian from
0:51
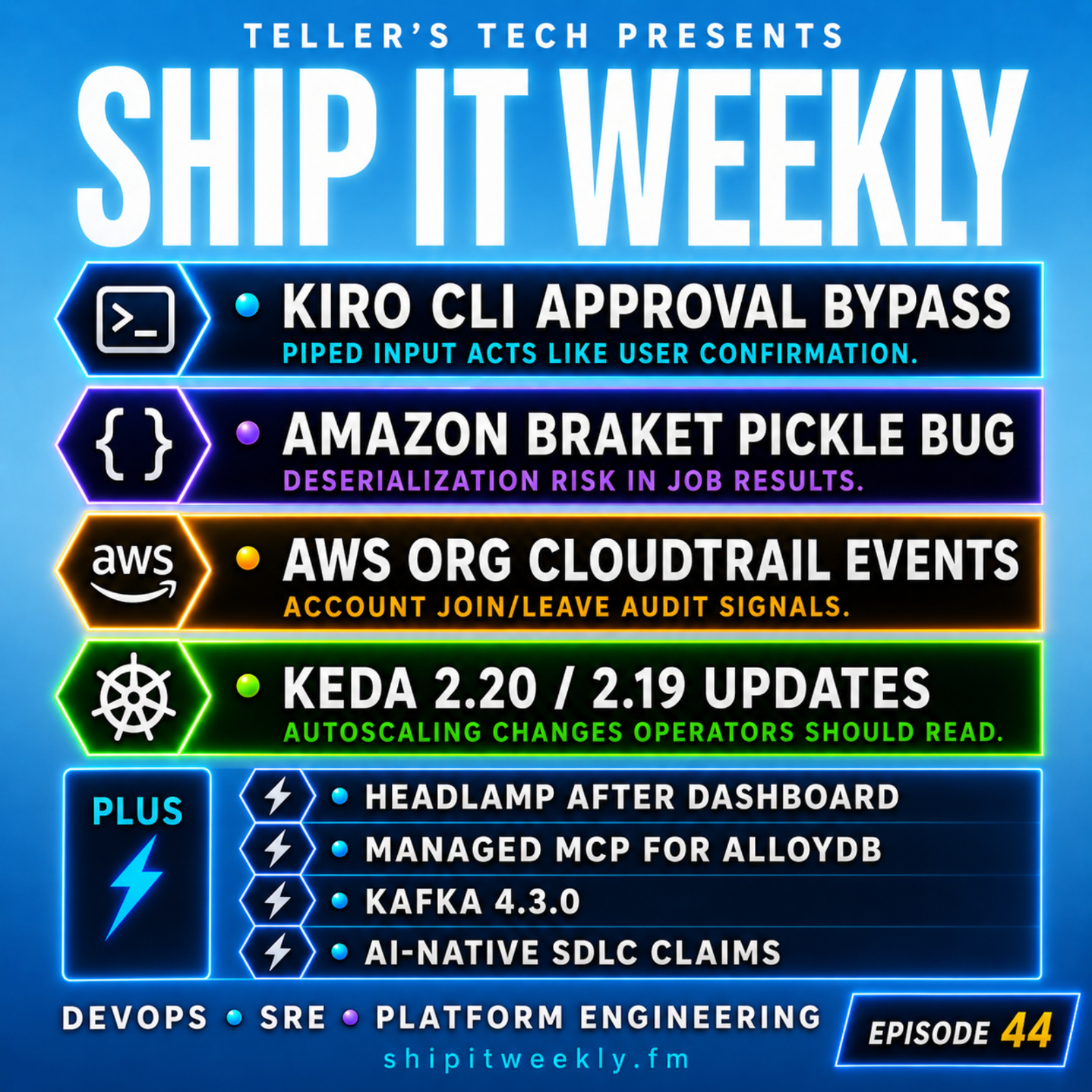
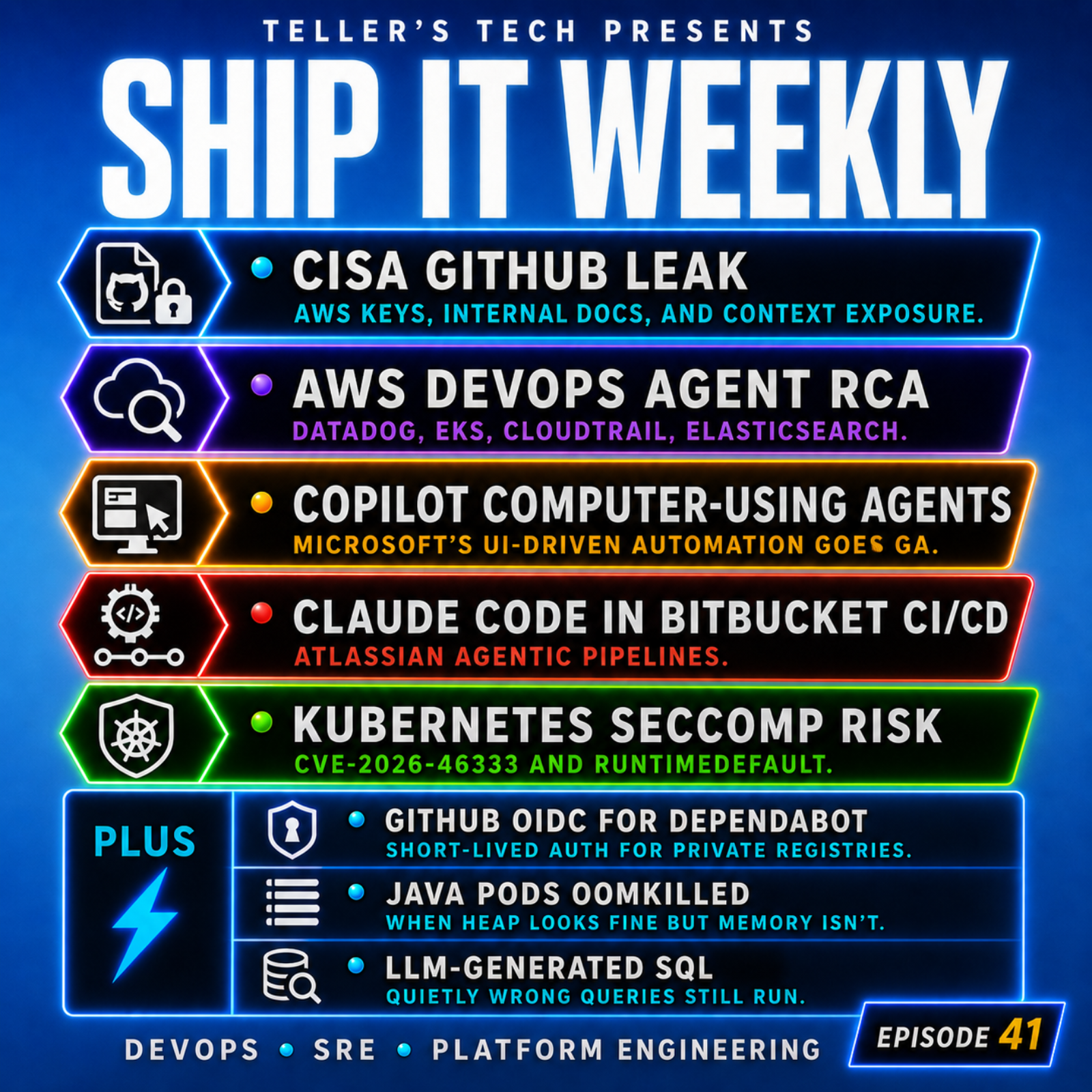
Tellers Tech and this is Ship It Weekly. You
0:54
can find full show notes, links, and past episodes
0:57
at shipitweekly .fm. And if you've been getting
1:00
value out of the show, subscribe wherever you
1:03
listen and leave a rating or review. It really
1:07
does help. Today is a special, just one topic,
1:10
Claude Mythos Preview, Project Glasswing, and
1:14
what this might mean for business, security,
1:17
and the way we think about DevOps. cloud, infra,
1:20
and the platform risk if this is even half as
1:23
meaningful as it looks. So let's start with the
1:31
obvious question. Why is this worth a special?
1:34
Because this does not feel like a normal model
1:37
launch story. Anthropic is not framing mythos
1:40
like, hey, the coding benchmark went up again.
1:43
They are framing it more like a threshold event
1:45
for security. And that gets my attention. Not
1:48
because I want to do the usual AI doom spiral
1:50
thing, but because if offensive capability really
1:54
is getting faster and cheaper, then that changes
1:57
the operating assumptions underneath a lot of
1:59
how companies run software. That is the part
2:02
I care about. Not the hype cycle, not the branding,
2:06
not whether people on LinkedIn are going to overreact
2:09
for two weeks. I care about what this means if
2:12
you run systems for a living. If you are the
2:14
person dealing with cloud sprawl. Aging workloads,
2:18
risky exceptions, strange identity boundaries,
2:21
rollout safety, patch friction, and all the messy
2:25
stuff real companies carry around for years.
2:28
That is why this is worth a special. Because
2:31
this is not really an AI story. It is an infrastructure
2:34
risk story. It is a tempo story. It is a story
2:38
about what happens if exploit discovery starts
2:42
moving at machine speed while most engineering
2:44
organizations are still patching, approving,
2:47
and modernizing at human speed. And before we
2:56
go deeper, I want to do a callback to our OpenClaw
2:59
special for a second. That episode was really
3:02
about what happens when Agent Tolling stops being
3:05
a toy and starts acting like a control plane.
3:08
Real tokens. Real permissions. Real blast radius.
3:12
That was the point. This Mythos story is different,
3:15
but it rhymes. OpenClaw was about what happens
3:18
when we give software more autonomy inside messy
3:21
environments. Mythos is about what happens when
3:24
the capability to find weaknesses in those environments
3:27
and chain those weaknesses together starts scaling
3:31
faster too. So I would not call this a sequel
3:34
to OpenClaw, but I do think it lives in the same
3:37
broader theme. Software is getting more capable.
3:40
Attack surfaces are getting weirder. And the
3:43
control planes around us are not always as sturdy
3:46
as we pretend they are. So what actually happened?
3:55
Anthropic released Claude Mythos Preview, not
3:58
as some big open general release, not as a fun
4:01
playground feature. It paired it with something
4:03
called Project Glasswing, which is clearly being
4:06
positioned around defensive cybersecurity and
4:09
critical software protection. That alone tells
4:12
you a lot. Because release posture matters. Companies
4:16
tell on themselves a little bit by how they ship
4:18
things. And when the release pattern looks more
4:21
like we should probably be careful with this,
4:24
that is worth paying attention to. Now, I want
4:26
to be honest here. A lot of the detailed evidence
4:29
right now still comes from Anthropic itself.
4:32
So this is not one of those stories where we
4:35
have 20 independent teardown articles and a full
4:38
year of real -world data. We do not. And that
4:41
means you should not just swallow every claim
4:43
whole. But I also think the dumb response is
4:46
to roll your eyes and call it marketing and move
4:48
on. Because even if you discount the loudest
4:51
version of the story, the direction of the story
4:53
is pretty clear. These models are getting better
4:56
at the kind of patient, iterative, technical
4:58
reasoning that matters a lot in security work.
5:01
Reading code, testing ideas, trying paths, rejecting
5:05
dead ends. following weird clues, chaining small
5:09
mistakes into bigger outcomes. That is not a
5:12
toy capability. That is exactly the kind of work
5:15
defenders and attackers both care about. And
5:23
this is where I think the smart posture sits.
5:25
Do not get gullible, but also do not get lazy.
5:28
Those are two different mistakes. Getting gullible
5:31
means repeating every claim like it is already
5:34
fully proven and independently validated. I do
5:37
not think this is reasonable. Getting lazy means
5:40
hearing something uncomfortable and dismissing
5:43
it because it sounds too dramatic or too early.
5:46
I do not think that is smart either. The better
5:48
middle ground is this. Maybe the headline version
5:51
gets softened over time. Maybe some details get
5:54
revised. Maybe some of the early framing turns
5:57
out to be too strong. Okay, fine. But if the
6:00
core trend is real, and I think it probably is,
6:03
then the implication is still serious. The implication
6:06
is not that AI suddenly invented security problems.
6:10
The implication is that it may be making parts
6:12
of offensive security cheaper, faster, and more
6:16
scalable. And once that starts happening, messy
6:19
organizations pay for it first. That is the key.
6:22
Messy pays first. Not necessarily the company
6:25
with the most code. Not necessarily the company
6:28
with the fanciest stack. The company with the
6:30
most weak assumptions, slow cleanup, fuzzy ownership,
6:34
and chainable mistakes. That is who pays first.
6:42
So let's talk about what changes if this is even
6:45
half true. Not all true, half true. What changes?
6:48
Well, for one, platform debt becomes attacker
6:51
leverage. That old base image you have not refreshed?
6:55
That broad deploy role nobody wanted to narrow.
6:57
That weird internal service that still trusts
7:00
way too much. That forgotten runner. That weird
7:03
path with too much access. That long -lived secret.
7:06
That temporary exception that turns two years
7:09
old. Those things do not just sit there as background
7:11
ugliness anymore. They become easier to discover,
7:14
easier to reason about, and possibly easier to
7:17
combine. And that combination part matters. Because
7:20
most real incidents are not about one perfect
7:23
movie villain bug. They are about a chain, a
7:26
little access here, a weak boundary there, too
7:29
much trust somewhere else, an old dependency,
7:32
a stale assumption, a permission that never got
7:35
revisited. That is how real environments break.
7:38
So if a model gets better at following those
7:41
threads with patience and speed, the problem
7:44
is not just vulnerable code. The problem is vulnerable
7:47
operating models. That is the line that I keep
7:50
coming back to, not vulnerable apps. vulnerable
7:53
operating models. Because a lot of companies
7:56
do not have a pure software problem. They have
7:59
a systems problem. And this is also why this
8:07
is not just for AppSec people or weird infra
8:10
nerds like me. Business leaders should care too.
8:13
Because if exploit discovery gets cheaper, then
8:17
risk math changes. Vendor risk changes. Cyber
8:20
insurance assumptions change. Patch service level
8:23
exceptions change. Acquisition diligence changes.
8:27
Third -party component trust gets more fragile.
8:29
Legacy systems become more dangerous to leave
8:32
alone. And once you get into regulated industries
8:35
or older enterprises, this gets even more interesting.
8:39
Because a lot of those environments are not clean.
8:42
They are layered. Modern things on top of old
8:46
things. Cloud native things next to brittle things.
8:49
Shared dependencies. Inherited architecture.
8:52
Historical compromises. Basically, every mature
8:55
company has some version of this. Which means
8:59
the real business question is not, should we
9:01
be scared of mythos? The better question is,
9:04
are we still operating like offensive capability
9:06
is scarce, expensive, or relatively slow? Because
9:11
if that assumption is weakening, then defensive
9:13
speed becomes more valuable. Inventory becomes
9:17
more valuable. Rollback confidence becomes more
9:20
valuable. Privilege reduction becomes more valuable.
9:23
And isolation becomes more valuable. That changes
9:26
how you think about maturity. It stops being
9:28
polish. It becomes resilience. Now let's bring
9:37
this back to our world. What does this mean for
9:39
DevOps, cloud, platform, and infra teams? Honestly,
9:43
it means a lot of the boring stuff just got more
9:46
important. And I know that is not the sexy answer,
9:49
but it is the real answer. If you run platform
9:52
or infra, your job is not just uptime and throughput
9:55
and deployment velocity. Your job is also making
9:59
it harder for mistakes to connect. That is the
10:02
lens. Make it harder for mistakes to connect.
10:05
That means looking hard at identity boundaries.
10:08
Do we have roles that are broader than they need
10:10
to be? Do our pipelines have access they should
10:13
not have? Can one compromise in one place turn
10:16
into access somewhere much more sensitive? That
10:19
means looking at credentials. Where do long -lived
10:22
credentials still exist? Where are secrets exposed
10:24
to more systems than necessary? Where are we
10:28
still relying on convenience over containment?
10:31
That means looking at old compute and images.
10:34
How stale are our base images? How stale are
10:36
our AMIs? How many things are running because
10:39
nobody wants to touch them? How many self -hosted
10:42
utilities are basically just squatting in the
10:45
environment and hoping nobody notices? That means
10:48
looking at network boundaries and trust assumptions.
10:50
What internal services are reachable too broadly?
10:53
What dashboards, admin surfaces, or support tooling
10:57
have drifted into being more exposed than anyone
11:00
intended. What old assumptions about internal
11:03
means safe are still hanging around. And it means
11:06
looking at rollout safety because patching speed
11:09
only matters if patching is survivable. If every
11:13
patch feels like a mini heart attack because
11:15
rollout is fragile and confidence is low, then
11:18
your organization is going to move too slowly
11:21
exactly when slow movement starts costing more.
11:25
That, to me, is the DevOps angle. Not AI will
11:28
replace security engineers, no. This is more
11:31
like the value of disciplined infrastructure
11:33
and safer defaults just went up. I keep coming
11:41
back to this phrase because I think it is the
11:44
practical takeaway. Boring work just got promoted.
11:47
Inventory, golden paths, patch automation, safer
11:51
defaults, ephemeral credentials, cleaner ownership.
11:54
Faster rollback. Less standing privilege. Better
11:58
dependency visibility. Tighter separation between
12:00
build, deploy, secrets, and runtime. That stuff
12:04
is not glamorous. Nobody wants to do some chest
12:07
-thumping keynote about cleaning up permissions
12:09
in some ugly deployment path. But this is exactly
12:12
the kind of work that matters if the cost curve
12:15
on offense is moving. Because when offense gets
12:18
cheaper, defenders do not win by being more dramatic.
12:21
They win by being less sloppy. Less trust. Less
12:25
drift. Less ambiguity. Less hidden blast radius.
12:29
This is not as fun to talk about as something
12:31
big AI changes everything narrative. But it is
12:34
the part that actually helps. So here's the uncomfortable
12:42
takeaway. For years, security people have said
12:45
defenders have the hardest job because defenders
12:47
have to protect everything and attackers only
12:50
need one path. That asymmetry is not new. what
12:53
might be changing is the cost of finding that
12:56
path. That is the part worth sitting with. If
12:59
finding and chaining exploitable paths gets cheaper,
13:02
then the old enterprise habit of living with
13:04
moderate mess becomes a worse bet. We'll get
13:08
to it next sprint. We should clean that up this
13:10
quarter. Nobody really owns that, but it still
13:13
works. We know the role is broad, but tightening
13:15
it would take time. That thing is ugly, but touching
13:18
it is risky. Those are all normal enterprise
13:20
sentences, and they may be getting more expensive.
13:23
That is really what this episode is about. Not
13:26
panic, not hype, not AI fanfiction. Just a sober
13:30
possibility. The exploit timeline may be collapsing
13:33
faster than the enterprise cleanup timeline.
13:35
And if that is true, then platform maturity is
13:38
not cleanup work anymore. It is frontline security
13:41
work. That is the shift. So if I were talking
13:49
to a platform team or engineering leadership
13:52
right now, I would not say panic. I would say
13:55
go look where your environment is embarrassingly
13:57
chainable. That is the phrase. Embarrassingly
14:00
chainable. Not just what has a critical CVE.
14:03
Not just what your scanner painted red this week.
14:06
Look for where mistakes connect too easily. Can
14:10
someone go from an internet -facing thing to
14:12
an internal thing too easily? Can someone pivot
14:15
from CI to secrets too easily? Can someone inherit
14:18
cloud access they never should have had? Can
14:21
one weird old service become a bridge into something
14:24
much more important? Do you actually know what
14:27
is exposed? Do you actually know what is privileged?
14:30
Do you actually know what would be painful to
14:33
patch fast? That is where I would start. And
14:36
then I would ask the harder question. What cleanup
14:39
work have we been treating like optional that
14:42
maybe is not optional anymore? Because let's
14:44
be honest. Most companies do not need a frontier
14:47
model to tell them their permissions are too
14:50
broad, their dependencies are stale, their ownership
14:53
is fuzzy, and their patching process is slower
14:56
than it should be. They already know that. The
14:58
real question is whether the cost of leaving
15:00
that mess alone is going up. I think it probably
15:03
is. So to wrap this up, mythos might turn out
15:06
to be a true inflection point. It might also
15:09
turn out that some of the early narrative gets
15:11
revised as more evidence comes out. Those things
15:14
are not mutually exclusive. But if you work in
15:17
DevOps, SRE, cloud, or platform engineering,
15:21
the useful takeaway is pretty much the same either
15:23
way. Assume your messy edges matter more. Assume
15:26
your platform maturity is security work. Assume
15:29
rollback, repair, and isolation matter even more
15:33
than before. And assume we'll get to it later
15:36
is getting riskier. That is the lesson that I
15:38
would keep. Not fear, not hype, just this. If
15:42
offensive capability is speeding up, then defensive
15:45
maturity has to stop being treated like optional
15:48
cleanup. The full show notes and links for this
15:51
episode are on shipitweekly .fm. And if this
15:54
episode got your brain moving a little bit, subscribe
15:57
to the show wherever you listen. Follow, rate,
16:00
review, share it with somebody who runs infra,
16:02
security, or engineering. That stuff really does
16:05
help. I'm Brian from Tellers Tech, and this has
16:08
been Ship It Weekly. Thanks for listening, and
16:11
I'll see you next time.